Confidentiality in Event Tech: Is Your Data Secure?
Corporate event planning involves managing a vast amount of sensitive information. From attendee PII (personally identifiable information) and VIP travel details to confidential launch strategies and budget breakdowns, the data you handle is a high-value target. As planning becomes more digitized, ensuring the security and confidentiality of this event data isn’t just a best practice—it’s a critical responsibility.
Yet, many event management workflows remain vulnerable. Scattered spreadsheets, endless email chains, and a patchwork of single-purpose apps create significant security gaps. For corporate planners, a data breach can lead to serious consequences, including financial loss, reputational damage, and legal penalties.
Understanding these risks is the first step toward building a more secure planning process. This guide will walk you through common vulnerabilities in event technology, what to look for in a secure platform, and how a centralized system can become your strongest defense in protecting sensitive event data.
Common Vulnerabilities in Event Planning
In a typical planning cycle, data flows through numerous channels, often with inconsistent security measures. This fragmented approach creates multiple points of failure where confidentiality can be compromised.
The Problem with Scattered Tools
When your team relies on a mix of disconnected tools—like spreadsheets for budgets, Word documents for run-of-show, and various messaging apps for communication—you lose centralized control. Data is duplicated, downloaded to personal devices, and shared through insecure channels. It becomes nearly impossible to track who has access to what information, creating a significant risk for your event data security.
Consider this common scenario: a crucial budget file is emailed back and forth between team members. Each email creates a new version of the file on different servers and local machines. If one of those accounts is compromised or a laptop is lost, that sensitive financial data is exposed.
Human Error and Inconsistent Protocols
Even with the best intentions, human error remains a leading cause of data breaches. A team member might accidentally share a file with the wrong person or use a weak, easily guessable password. Without standardized security protocols enforced by a central system, each person becomes a potential point of vulnerability. This risk is magnified when working with external vendors and temporary staff who may not follow your organization’s internal security policies.
What to Expect from Your Event Technology
To effectively protect your data, your event technology must be built with security at its core. When evaluating a platform, corporate planners should prioritize several key features that ensure data confidentiality and integrity.
Centralized Version Control
A robust system eliminates the chaos of multiple file versions. Instead of emailing documents, your team should work from a single, cloud-based source of truth. Every change is tracked, and a clear history of edits is maintained. This ensures everyone is working with the most current information and prevents outdated or incorrect data from causing costly mistakes. Version control also provides an audit trail, showing who made changes and when, which is crucial for accountability and post-event analysis.
Granular Permissions Models
Not everyone on your team needs access to every piece of information. A secure event management platform should allow you to set granular, role-based permissions. This means you can control who can view, edit, and share specific files or data sets.
For example:
- Event Leads can have full administrative access to view budgets, vendor contracts, and strategic documents.
- Creative Teams can be given access to content and branding files but restricted from financial information.
- External Vendors can be granted limited access only to the specific documents relevant to their services, such as AV specs or venue layouts.
This model of “least privilege access” is a cornerstone of effective event data security. It minimizes the risk of accidental exposure and ensures that sensitive information is only accessible on a need-to-know basis.
How Event Alchemē Prioritizes Security
Understanding these security imperatives is why we built Event Alchemē, our custom event management portal. It was designed from the ground up to provide corporate planners with a secure, centralized, and efficient workspace that protects sensitive data throughout the entire event lifecycle.
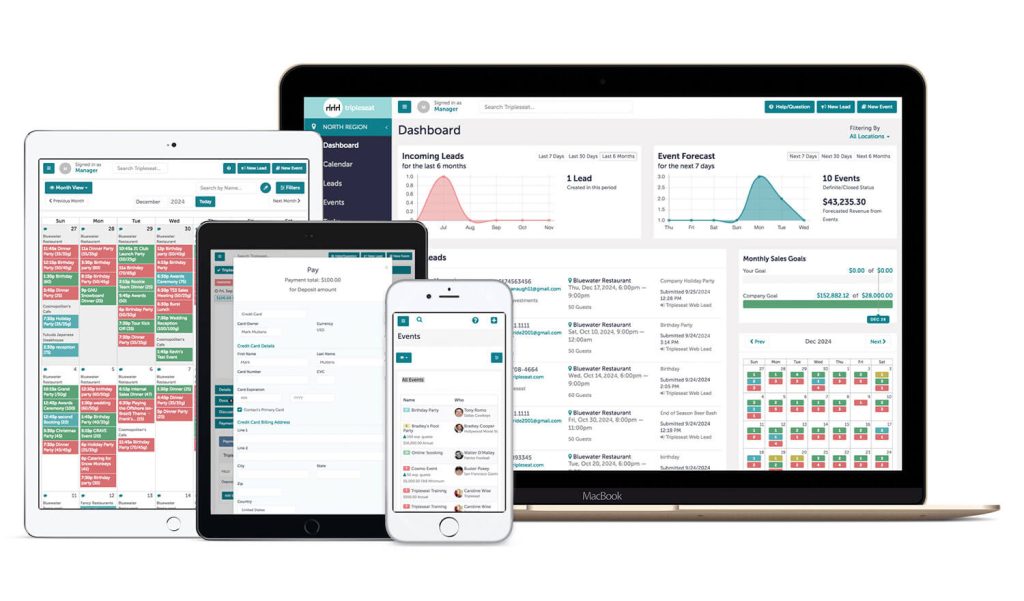
Event Alchemē is not just another tool; it’s a secure ecosystem tailored to your team’s specific workflow. By replacing scattered spreadsheets and email threads with a unified command center, we address the core vulnerabilities inherent in traditional planning methods.
Our platform’s security posture is built on key principles:
- Centralization: All your event data—from task management and vendor tracking to budgets and timelines—lives in one secure, access-controlled environment. This eliminates data silos and reduces the attack surface.
- Custom Permissions: We work with each client to configure a bespoke permissions model that aligns with their organizational structure and security policies. You have complete control over who sees what, ensuring confidentiality is maintained at every level.
- Version Control: With Event Alchemē, your team always works from the latest version of every document. The system automatically tracks changes, creating a transparent audit trail and preventing errors that arise from using outdated information.
- Secure Collaboration: Our integrated collaboration features allow your team and external partners to communicate and share files within the portal, ending the reliance on insecure email attachments and third-party messaging apps.
By consolidating your workflow into a single, secure platform, Event Alchemē helps you operate with the confidence that your sensitive data is protected.
A New Standard for Event Data Security
As the complexity of corporate events grows, so do the risks associated with managing sensitive data. Relying on a patchwork of tools and inconsistent processes is no longer a viable option for planners who are serious about confidentiality. The potential for a data breach is too high, and the consequences too severe.
Adopting a centralized, secure event management platform is the most effective way to mitigate these risks. By implementing features like granular permissions and robust version control, you can create a fortified environment that protects your data, streamlines your workflow, and empowers your team to focus on what they do best: creating exceptional events.
If you’re ready to elevate your event data security and bring a new level of efficiency to your planning process, learn more about how Event Alchemē can be tailored to your organization’s needs.